Cybersecurity is on everyone's minds, and it starts from the inside for many businesses. Insiders are often responsible for data breaches — accidental and intentional — so robust authentication and authorization are a must. While authentication and authorization are two sides of the same access management coin, a thorough understanding of how they work is essential to enhance your cybersecurity.
Knowing how authentication is different from authorization elevates your security beyond simple access management. It helps you implement a comprehensive approach to keeping cybercriminals at bay.
In This Article
- What is Authentication?
- Authentication Methods
- What is Authorization?
- Authorization Methods
- What's the Difference Between Authentication and Authorization?
- The Role of Authentication and Authorization in a Zero Trust Framework
- Strengthen Your Authentication and Authorization Strategy with Bravura Security
What Is Authentication?
Authentication is the security process by which the identity provided by a user is recognized and verified to prove they are who they claim to be. When accessing an app or network, you must verify your identity with an authentication method like a password or passwordless authentication options such as biometrics.
Authentication can verify users, processes and devices. Depending on your business's authentication strategies, it can give you a robust first checkpoint in your cybersecurity profile. Almost all industries use authentication as part of their security, from retail staff accessing point-of-sale systems to high-security data centers protecting valuable data assets. Regardless of the business, confirming someone's identity is a fundamental step to keeping your digital assets safe.
Authentication Methods
Businesses can use several methods to authenticate people and devices, depending on the level of security, the number of employees and several other factors. You can break all forms of authentication down into three main groups:
- What you have: Users can authenticate themselves with a personal possession, such as a mobile phone application, ID card or security token.
- What you know: This could be a password, a security question or a PIN.
- What you are: This authentication method relies on users' physical traits, such as fingerprints, retina scans and facial recognition.
Many organizations choose to employ a combination of authentication methods. This Multifactor Authentication (MFA) gives you an extra layer of security by combining biometrics, passwords, devices and even location and behavior to have a detailed approach to verifying that users are whom they claim.
Single Sign-On (SSO) is another common authentication method. It lets users log in to one application to access other applications. It's convenient, low friction and often relies on an Identity and Access Management (IAM) system that creates secure links between applications.
What Is Authorization?
Authorization allows authenticated users to access applications or resources within your network based on their roles. In any business, there are varying levels of information, from public data on your website and internal communication for employees to confidential information for management. Authorization — or access management — allows the appropriate people to access the necessary levels of information.
Once you know a person is who they say; you can decide what resources they need to access and then grant them the appropriate permissions. In essence, authorization is the foundational concept that underpins access control strategies, and enables you to add layered security for users according to their duties and seniority.
The authorization process should always follow authentication to give your business the highest level of cyber security. Users must confirm their identities before their administrators decide whether there's a need to grant them access to specific functions and resources.
Authorization Methods
Like authentication, several methods exist to authorize users and grant them the appropriate permissions. Businesses can use one or a combination of authorization methods to elevate their security profile. Some standard authorization methods include the following:
- Role-Based Access Control (RBAC): With RBAC, users can access information based on their role in your organization. Your employees may be able to view information on a particular project, such as budget requirements, and management could have access to the information with the option to change or delete data. This authorization method lets users stay productive and controls sensitive data access. RBAC is ideal for organizations with well-defined roles where access needs are consistent and can be grouped efficiently into these roles.
- Attribute-Based Access Control (ABAC): ABAC is an excellent tool to limit user access further. Users are granted access to information based on a series of attributes, including their role, security clearance, location, time of access and even your business's current threat level. With access dependent on qualifiers like the time of day or a user's geographical location, you can maintain robust security protocols throughout your organization. ABAC is best suited for complex, dynamic environments where access decisions depend on a wide range of factors and contexts.
- Policy-Based Access Control (PBAC): PBAC is an effective method of managing user access to multiple systems. It combines users' attributes - like business titles - with policies to determine which access privileges users should have. The system compares theoretical privileges to actual privileges and applies the differences automatically. This approach simplifies access control by focusing on clear policies, making it less complex but potentially less granular than attribute-based methods like ABAC. PBAC is suitable for environments where access control can be broadly managed through comprehensive and well-defined policies.
What's the Difference Between Authentication and Authorization?
Understanding the difference between authentication and authorization is essential for your security strategy. They're both essential tools in your business's security approach. Although the two protocols can work together, some key areas show how authentication differs from authorization, including the following:
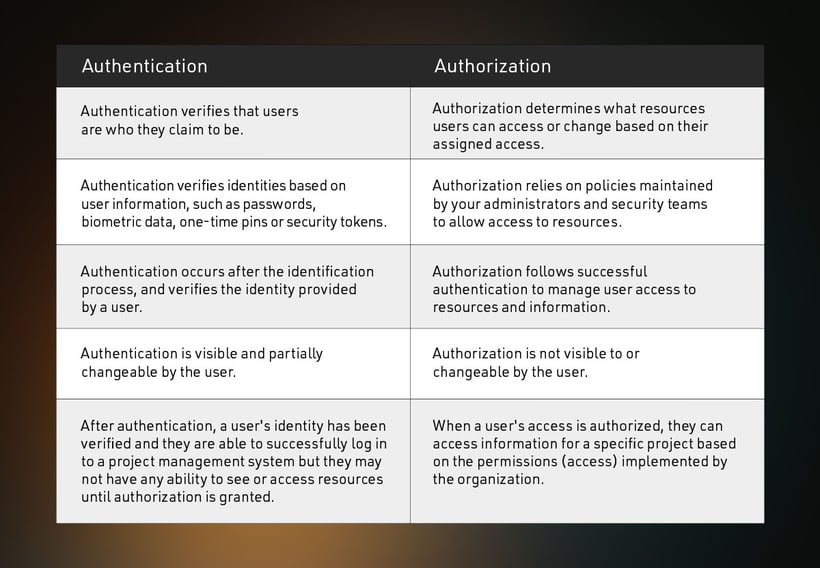
What Is Its Purpose?
- Authentication verifies that users are who they claim to be.
- Authorization determines what resources users can access or change based on their assigned access.
How Does It Work?
- Authentication verifies identities based on user information, such as passwords, biometric data, one-time pins or security tokens.
- Authorization relies on policies maintained by your administrators and security teams to allow access to resources.
When Does It Happen?
- Authentication occurs after the identification process, and verifies the identity provided by a user.
- Authorization follows successful authentication to manage user access to resources and information.
Who Controls It?
- Authentication is visible and partially changeable by the user.
- Authorization is not visible to or changeable by the user.
Examples
- After authentication, a user's identity has been verified and they are able to successfully log in to a project management system but they may not have any ability to see or access resources until authorization is granted.
- When a user's access is authorized, they can access information for a specific project based on the permissions (access) implemented by the organization.
The Role of Authentication and Authorization in a Zero Trust Framework
A zero trust framework operates on a straightforward premise — always verify. As technology has evolved, the paradigm of centering cyber security around a specific location has become obsolete. Employees need to access their organization's networks from home or while on the move.
A zero trust security strategy requires all users to be authenticated, authorized and consistently validated before they can access applications and data. It gives businesses a robust solution to attempts at unauthorized access and layers of security so unauthorized users can't access your organization's sensitive data if there is a breach.
The Enhanced Identity Governance approach to Zero Trust proposed by the National Institute of Standards and Technology (NIST) focuses on access policies which are based on identity and assigned attributes. Strong authentication coupled with privileged access management and identity management are foundational to this approach. Securing access to data and resources in this model ultimately rely on the ability to authenticate the subject and approve the request before granting access to make policy decisions. Authentication and authorization form part of a unified platform to create identity-based security cohesiveness.
Strengthen Your Authentication and Authorization Strategy with Bravura Security
Effective cyber security means using every resource to stay ahead of ever-changing threats. Combining a zero trust framework, Privileged Access Management like Bravura Privilege with robust Identity Access Management services and cutting-edge innovations like Bravura OneAuth is the ideal multilayered approach to enhancing your organization's overall cyber security.
Transform your digital identity and access security with the Bravura Security Fabric — the only IAM software suite bringing these dynamic resource entitlement access management tools into one platform, providing users with the power of one solution. Request a demo today to learn more about how Bravura Security's innovations can benefit your business.
Related Articles
14 Types of Digital Authentication
Data security is one of the most critical elements of operations for many businesses. Authentication is a fundamental cybersecurity concern, with up to 80% of attacks on...
The Pros and Cons of Passwordless Authentication
Cybersecurity threats are a serious concern for businesses, and with 81% of breaches resulting from hacked or stolen passwords, companies must explore alternative...
What Is True Passwordless Authentication?
The digital landscape has changed and the authentication techniques we've relied on for years have given way to faster and more secure solutions. Still, one thing...
