What Is PAM and Why Do You Need It?
What Is Privileged Access Management?
Privileged Access Management or “PAM” is a cybersecurity term that refers to the strategies, policies and technologies an organization uses to manage privileged access and permissions. This privileged access is a user's ability to access resources ordinary users can't and typically includes access to sensitive information and mission-critical systems. For example, an IT specialist needs more privileges than the average employee.
A PAM solution condenses your attack surface, which benefits your organization in the following ways:
- Reduces your risk of attack.
- Minimizes potential damage of an attack.
- Protects against privilege misuse.
PAM technologies also allow your admins to monitor and control user activity to prevent negligence, human error or malicious attacks before they can become a problem.
IAM vs. PAM vs. PIM
PAM is a key component of Identity Access Management (IAM), which identifies and authorizes users within your organization. As part of an IAM system, PAM focuses specifically on limiting user access to only the resources necessary for completing a user's duties. It also provides an audit trail that allows IT security teams to quickly respond to incidents if any occur.
Other components of PAM include:
- Privileged Identity Management (PIM): While PAM and PIM are often used interchangeably, PIM specifically focuses on managing resources rather than users' access to those resources.
- Privileged Session Management (PSM): PSM is a feature of advanced PAM tools that allows administrators to monitor what privileged accounts are doing. PSM capabilities often include workflow coordination, RDP and SSH logging and remote session monitoring.
How Does Privileged Access Management Work?
PAM works by enforcing the Principle of Least Privilege (PoLP), which means restricting employee access and permissions to the minimum level required to complete their jobs. Here are some examples of how privileged access management works:
1. Managing Access Privileges
Establishing least-privilege access for every account in your system helps you shrink your attack surface. This effort reduces the possible entry points for external attackers and lowers your risk of harm from external actors. It also decreases the chances that human error from inside the organization will result in serious damage.
Additionally, a PAM solution stores privileged account credentials and secrets in a secure central vault to prevent against cyberattacks. Users across the enterprise can send Just-In-Time (JIT) passwords for limited access, encryption keys and more without needing to worry about information getting leaked. This safe may be an integration with another software or another component of the PAM solution.
2. Offering Security for All Employees
As more companies shift toward hybrid and remote-first workforces, they adopt more third-party tools and services. These employees connect to work systems from many different locations, sometimes even from across the world.
This kind of work structure often requires that privileged machine accounts outnumber human employees. While a VPN can suffice for securing user access, organizations need a more granular solution to truly secure access to their cloud environments.
3. Monitoring Privileged User Activity
Without a PAM solution in place, privileged users often operate without visibility outside the specific tool or asset they're using. PSM enables your admins to observe what every privileged user in your network is doing, so they can easily find and respond to issues in real time.
Additionally, PSM helps simplify your auditing and compliance requirements, enabling your organization to more easily comply with cybersecurity and industry regulations, such as HIPAA, GDPR and ISO 27001.
Types of Privileged Accounts
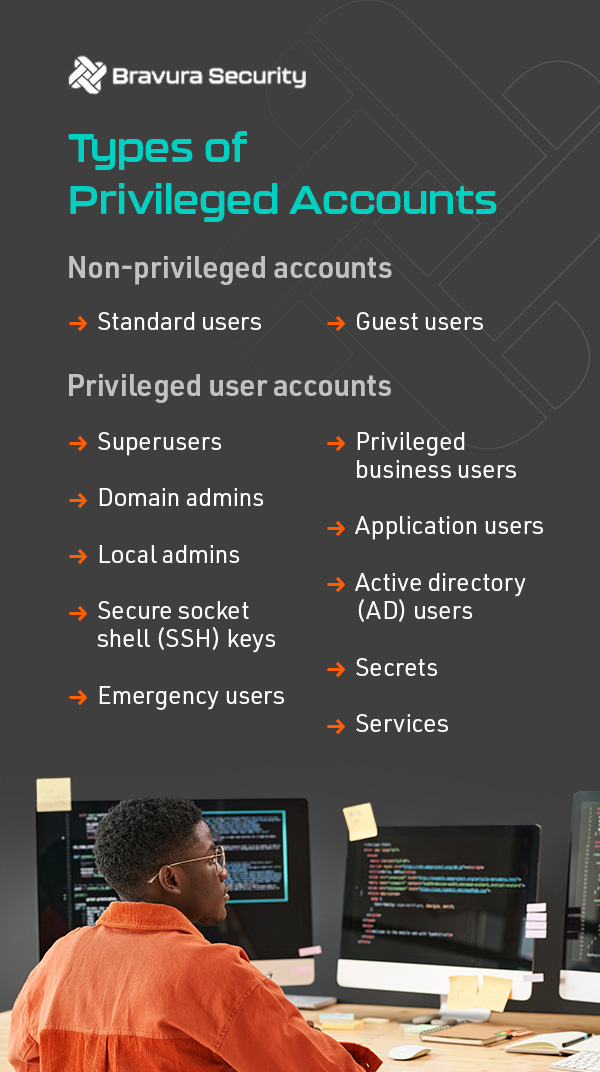
It's important to define the difference between privileged and non-privileged accounts. While privileged accounts have access to advanced or elevated privileges, non-privileged accounts are all other accounts that lack high-level permissions.
The two types of non-privileged accounts include:
- Standard users: These typical business user accounts provide access to only what they need to do their jobs, such as internet browsing, SaaS tools, email and word processing applications.
- Guest users: These accounts have extremely limited privileges, such as basic access to internet browsing and applications.
There are many types of privileged user accounts, and they can apply to cloud or on-premise applications. For example, your social media director may need privileged access to your organization's cloud-based social profiles, while IT specialists may need privileged access to local computers.
The most common types include:
- Superusers: Also known as a root, supervisor or admin account, a superuser account has the most expansive privileges. These users can make changes to your system, execute commands and adjust permissions for other users.
- Domain admins: This Windows account can modify the active directory in ways such as changing user permissions and creating and deleting users.
- Local admins: Although a local admin can access and modify a local Windows computer, they lack the ability to modify the active directory.
- Secure Socket Shell (SSH) keys: These are access credentials system admins use similarly to usernames and passwords to implement Single Sign-On (SSO) systems. Like human users, automated processes can also use SSH keys to authenticate into your firewalls, switches and routers.
- Emergency users: In the event of a crisis, emergency accounts enable non-privileged users to override access controls in secure applications.
- Privileged business users: Those in privileged roles such as finance, human resources and marketing require more extensive access to sensitive information than most non-privileged users.
- Application users: These accounts provide access to your databases and enable them to grant access to other apps in your ecosystem.
- Active Directory (AD) users: AD accounts enable services to interact with your OS, organize your data and manage user and machine accounts.
- Secrets: This nickname refers to credentials, keys and tokens that allow both service and user accounts to enter privileged systems. Protecting your organization's secrets is a critical aspect of cybersecurity.
- Services: These are some of the highest-risk accounts in your environment and can interact with the OS, run scheduled tasks and make changes to your system.
Why Is PAM Important?
A comprehensive PAM solution reduces the risk of cyberattacks resulting from unmanaged accounts by:
- Allowing for better monitoring and control.
- Ensuring compliance with regulations.
- Ensuring a full audit trail of who had access to what resources.
- Preventing privilege creep.
- Eliminating the risk of privilege abuse.
- Managing and securing infrastructure accounts.
- Removing local admin rights on workstations.
By limiting the access privileges of your standard users, a robust PAM solution significantly reduces vulnerability for cloud, hybrid and on-premise systems. It also helps your organization more easily achieve compliance with critical industry and government regulations.
Privileged Access Management Implementation Best Practices
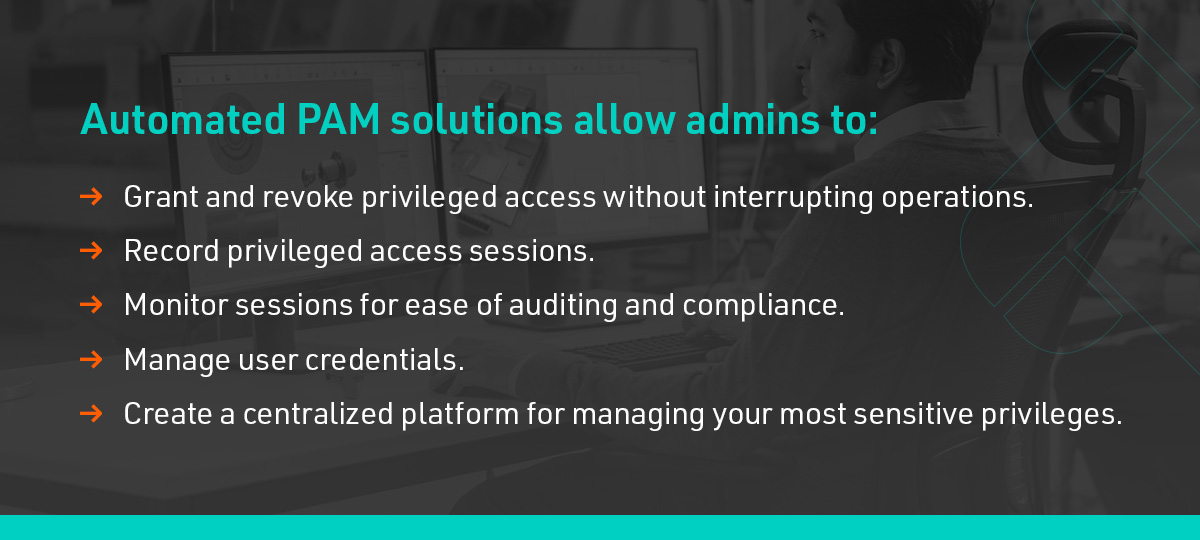
Using a manual system, such as spreadsheets, to track and manage privileged accounts is impractical for most modern business environments. That's why enterprises need to invest in automated PAM solutions. These tools allow admins to:
- Grant and revoke privileged access without interrupting operations.
- Record privileged access sessions.
- Monitor sessions for ease of auditing and compliance.
- Manage user credentials.
- Create a centralized platform for managing your most sensitive privileges.
Essentially, a next-generation PAM solution can manage privileges and accounts for you so your IT staff can focus on completing their day-to-day tasks.
Following PAM best practices can help make adopting a new solution simple. Consider the following when creating your implementation strategy:
1. Get C-Suite Buy-In
Relying on technology is rarely enough to make significant changes — every level of your organization needs to buy in to your solution. Getting the full support of your C-suite is especially important because your top executives determine what direction the whole company will take. When they fully buy in to your solution, they can effectively communicate your vision to the rest of your organization.
2. Create a Formal PAM Policy
Before anything else, you need to create a strong policy for your privileged access management solution. Create an ordered list of what privileges will cause the greatest impact on your organization if exploited. Who needs access to these privileges and for how long? These answers will inform different guidelines for your policy.
As with any policy change, documentation is key for lasting success. Clearly define each role in your organization and outline the privileges and access rights for each role. It's also important to set an expiry date for sensitive credentials like passwords, as doing so reduces the risk of attack and mitigates the potential impact of those attacks.
3. Take Inventory of All Third-Party Systems
Consistency is key for effective cybersecurity initiatives. Follow PoLP and limit privileged access across all your cloud applications, SaaS tools and other systems.
Require your employees to follow PAM policies when using any resource, whether it's an internal privilege or an external source. This is especially important when dealing with third-party vendors or independent contractors, as it can help prevent them from gaining access to unmanaged privileged accounts.
4. Follow Cybersecurity Best Practices

Tighten your existing security protocol by frequently rotating credentials, using SSO and implementing passwordless and Multi-Factor Authentication (MFA) solutions. These steps can reduce the risk of malicious actors gaining access to your system through stolen credentials.
Additionally, you'll want to regularly train your team on cybersecurity best practices to maximize your solution's potential effectiveness. Some important topics may include:
- Identifying and reporting phishing attempts.
- Creating strong passwords.
- Managing documents and other files.
- Eliminating password sharing.
Additionally, vault, rotate and manage secrets for both on-premise and cloud-based privileged accounts. Possible examples include machine learning environments, infrastructure automation platforms and containerization systems.
5. Enforce the Principle of Least Privilege
Limit access as much as possible for both service and user accounts. Entities should only be able to access the specific resources they need to fulfill their role.
Begin by auditing your entire environment to identify privileged accounts, then remove any unnecessary administrative privileges you find. Separate true privileged accounts from standard accounts and store their credentials in a highly secure digital vault to keep them safe.
To maximize privileged account protection, you can regularly rotate administrative credentials or enable time-limited access.

6. Get C-Suite Buy-In
Relying on technology is rarely enough to make significant changes — every level of your organization needs to buy in to your solution. Getting the full support of your C-suite is especially important because your top executives determine what direction the whole company will take. When they fully buy in to your solution, they can effectively communicate your vision to the rest of your organization.
7. Keep Policies Updated
Keeping your policies and procedures up to date prevents cybercriminals from taking advantage of outdated protocols. It's best to reevaluate your privileged access policies any time your organization experiences a significant change, such as:
- When your organization scales.
- When your organization restructures.
- When you adopt a new technology.
These changes are times when you're most likely to experience shifts in security and risk management requirements, which is why it's so important to regularly revisit your policies and update them to meet your evolving needs.

For more tips on successfully implementing PAM in a modern business environment, download our best practices e-book.
4 Reasons to Invest in a PAM Solution
An effective PAM initiative isn't always achievable with older products and services. The existence of legacy technology and various approaches mean the market for products that secure privileged accounts and related access rights is discordant. Current products can lack the scope and scale of facilities that large enterprises require.
Here are some top reasons why your organization should consider investing in a PAM solution.
1. Increased Transparency
Transparent security solutions are increasingly important for doing business in hybrid and fully remote environments. By guarding against unauthorized access and enabling admins to continuously monitor employee sessions, PAM solutions make managing your cybersecurity strategy painless.
2. Smooth Deployment
Unlike their predecessors, modern PAM solutions only require you to make minimal changes to your tech stack, processes and systems. From planning to implementation to deployment, getting started on a new PAM solution is easier than ever.
3. Reduced Threats to MSPs and MSSPs
Many enterprises have too many employees to reasonably manage their cybersecurity responsibilities themselves, which is why many outsource said tasks to Managed Service Providers (MSPs) and Managed Security Service Providers (MSSPs).
MSPs and MSSPs manage massive quantities of sensitive company data, which is why they're attractive targets for cyberattacks. Investing in PAM solutions can help you secure client endpoints and protect passwords, keeping your IT providers safe.
4. New Revenue Opportunities
PAM solutions make working across hybrid solutions smooth and simple. Advanced PAM software is highly scalable, so you can expand your business offerings and opportunities for revenue without needing to look for a new solution.
Protect Your Accounts With Bravura Security
PAM is an essential component of any IAM initiative. That's what makes Bravura Privilege, our advanced PAM solution, so beneficial to your tech stack. Bravura Privilege helps you tighten your organization's security policies by enabling frictionless access management, time-limited privileges, privileged session monitoring and more.
If you're ready to start your PAM journey, we're ready to help get you on your way. Request a demo to see our solution at work.
